QUESTION 101
What is one method that can be used to prevent VLAN hopping?
A. Configure ACLs.
B. Enforce username and password combinations.
C. Configure all frames with two 802.1Q headers.
D. Explicitly turn off DTP on all unused ports.
E. Configure VACLs.
Answer: D
QUESTION 102
Why is BPDU guard an effective way to prevent an unauthorized rogue switch from altering the spanning-tree topology of a network?
A. BPDU guard can guarantee proper selection of the root bridge.
B. BPDU guard can be utilized along with PortFast to shut down ports when a switch is connected to the port.
C. BPDU guard can be utilized to prevent the switch from transmitting BPDUs and incorrectly altering the root bridge election.
D. BPDU guard can be used to prevent invalid BPDUs from propagating throughout the network.
Answer: B
QUESTION 103
What two steps can be taken to help prevent VLAN hopping? (Choose two.)
A. Place unused ports in a common unrouted VLAN.
B. Enable BPDU guard.
C. Implement port security.
D. Prevent automatic trunk configurations.
E. Disable Cisco Discovery Protocol on ports where it is not necessary.
Answer: AD
QUESTION 104
Refer to the exhibit. Assume that Switch_A is active for the standby group and the standby device has only the default HSRP configuration. Which statement is true? 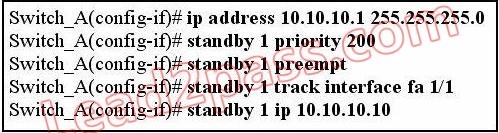
A. If port Fa1/1 on Switch_A goes down, the standby device takes over as active.
B. If the current standby device had the higher priority value, it would take over the role of active for the HSRP group.
C. If port Fa1/1 on Switch_A goes down, the new priority value for the switch would be 190.
D. If Switch_A had the highest priority number, it would not take over as active router.
Answer: C
QUESTION 105
When an attacker is using switch spoofing to perform VLAN hopping, how is the attacker able to gather information?
A. The attacking station uses DTP to negotiate trunking with a switch port and captures all traffic that is allowed on the trunk.
B. The attacking station tags itself with all usable VLANs to capture data that is passed through the switch, regardless of the VLAN to which the data belongs.
C. The attacking station generates frames with two 802.1Q headers to cause the switch to forward the frames to a VLAN that would be inaccessible to the attacker through legitimate means.
D. The attacking station uses VTP to collect VLAN information that is sent out and then tags itself with the domain information to capture the data.
Answer: A
QUESTION 106
When you create a network implementation for a VLAN solution, what is one procedure that you should include in your plan?
A. Perform an incremental implementation of components.
B. Implement the entire solution and then test end-to-end to make sure that it is performing as designed.
C. Implement trunking of all VLANs to ensure that traffic is crossing the network as needed before performing any pruning of VLANs.
D. Test the solution on the production network in off hours.
Answer: A
QUESTION 107
You have just created a new VLAN on your network. What is one step that you should include in your VLAN-based implementation and verification plan?
A. Verify that different native VLANs exist between two switches for security purposes.
B. Verify that the VLAN was added on all switches with the use of the show vlan command.
C. Verify that the switch is configured to allow for trunking on the switch ports.
D. Verify that each switch port has the correct IP address space assigned to it for the new VLAN.
Answer: B
QUESTION 108
Which two statements describe a routed switch port on a multilayer switch? (Choose two.)
A. Layer 2 switching and Layer 3 routing are mutually supported.
B. The port is not associated with any VLAN.
C. The routed switch port supports VLAN subinterfaces.
D. The routed switch port is used when a switch has only one port per VLAN or subnet.
E. The routed switch port ensures that STP remains in the forwarding state.
Answer: BD
QUESTION 109
Which two statements correctly describe VTP? (Choose two.)
A. Transparent mode always has a configuration revision number of 0.
B. Transparent mode cannot modify a VLAN database.
C. Client mode cannot forward received VTP advertisements.
D. Client mode synchronizes its VLAN database from VTP advertisements.
E. Server mode can synchronize across VTP domains.
Answer: AD
QUESTION 110
Which two DTP modes permit trunking between directly connected switches? (Choose two.)
A. dynamic desirable (VTP domain A) to dynamic desirable (VTP domain A)
B. dynamic desirable (VTP domain A) to dynamic desirable (VTP domain B)
C. dynamic auto (VTP domain A) to dynamic auto (VTP domain A)
D. dynamic auto (VTP domain A) to dynamic auto (VTP domain B)
E. dynamic auto (VTP domain A) to nonegotiate (VTP domain A)
F. nonegotiate (VTP domain A) to nonegotiate (VTP domain B)
Answer: AF
Passleader Actual Cisco 642-813 PDF & VCE Exam Dumps